As hospitals around the world are struggling to respond to the coronavirus crisis, cybercriminals—with no conscience and empathy—are continuously targeting healthcare organizations, research facilities, and other governmental organizations with ransomware and malicious information stealers.
The new research, published by Palo Alto Networks and shared with The Hacker News, confirmed that "the threat actors who profit from cybercrime will go to any extent, including targeting organizations that are in the front lines and responding to the pandemic on a daily basis."
While the security firm didn't name the latest victims, it said a Canadian government healthcare organization and a Canadian medical research university both suffered ransomware attacks, as criminal groups seek to exploit the crisis for financial gain.
The attacks were detected between March 24 and March 26 and were initiated as part of the coronavirus-themed phishing campaigns that have become widespread in recent months.
Palo Alto Networks' disclosure comes as The U.S. Department of Health and Human Services (HHS), biotechnology firm 10x Genomics, Brno University Hospital in the Czech Republic, and Hammersmith Medicines Research have been hit by cyberattacks in the past few weeks.
Delivering Ransomware by Exploiting CVE-2012-0158
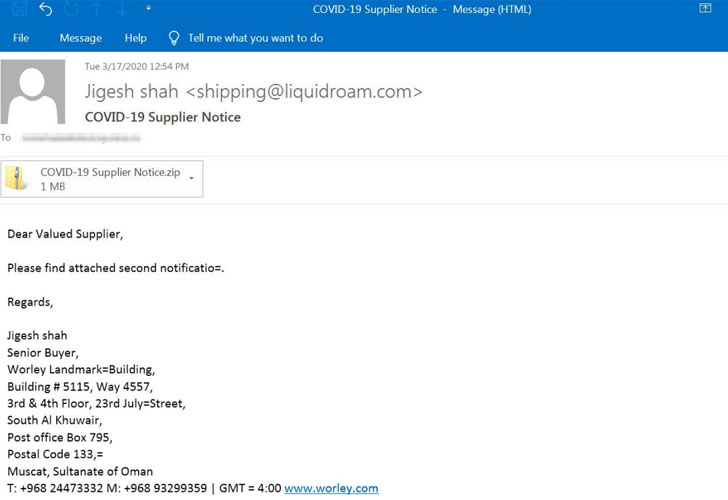
According to the researchers, the campaign began with malicious emails sent from a spoofed address mimicking the World Health Organization (noreply@who[.]int) that were sent to a number of individuals associated with the healthcare organization that's actively involved in COVID-19 response efforts.
The email lures contained a rich text format (RTF) document named "20200323-sitrep-63-covid-19.doc," which, when opened, attempted to deliver EDA2 ransomware by exploiting a known buffer overflow vulnerability (CVE-2012-0158) in Microsoft's ListView / TreeView ActiveX controls in MSCOMCTL.OCX library.
"It is interesting to note that even though the file name clearly references a specific date (March 23, 2020), the file name was not updated over the course of the campaign to reflect current dates," Palo Alto Networks researchers noted.
"It is also interesting that the malware authors did not attempt to make their lures appear legitimate in any way; it is clear from the first page of the document that something is amiss."
Upon execution, the ransomware binary contacts the command-and-control (C2) server to download an image that serves as the main ransomware infection notification on the victim's device, and subsequently transmits the host details to create a custom key to encrypt the files on the system's desktop with a ".locked20" extension.
Aside from receiving the key, the infected host uses an HTTP Post request to send the decryption key, encrypted using AES, to the C2 server.
Palo Alto Networks ascertained that the ransomware strain was EDA2 based on the code structure of the binary and the host-based and network-based behaviors of the ransomware. EDA2 and Hidden Tear are considered one of the first open-source ransomware that were created for educational purposes but have since been abused by hackers to pursue their own interests.
A Spike in Ransomware Incidents
The ransomware attacks are a consequence of an increase in other cyberattacks related to the pandemic. They have included a rash of phishing emails that attempt to use the crisis to persuade people to click on links that download malware or ransomware onto their computers.
Furthermore, Check Point Research's Brand Phishing Report for Q1 2020 observed a jump in mobile phishing due to people spending more time on their phones for information related to the outbreak and for work. Attackers were found imitating popular services such as Netflix, Airbnb, and Chase Bank to steal login credentials.
With hospitals under time constraints and pressure due to the ongoing pandemic, hackers are counting on the organizations to pay ransoms to recover access to critical systems and prevent disruption to patient care.
A report released by RisKIQ last week found that ransomware attacks on medical facilities were up 35% between 2016 and 2019, with the average ransom demand being $59,000 across 127 incidents. The cybersecurity firm stated that hackers also favored small hospitals and healthcare centers for reasons ranging from lean security support to increased likelihood of heeding to ransom demands.
The spike in ransomware attacks against the medical sector has prompted Interpol to issue a warning about the threat to member countries.
"Cybercriminals are using ransomware to hold hospitals and medical services digitally hostage, preventing them from accessing vital files and systems until a ransom is paid," the agency said.
To protect the systems from such attacks, Interpol cautioned organizations to watch out for phishing attempts, encrypt sensitive data, and take periodic data backups, aside from storing them offline or on a different network to thwart cybercriminals.






0 Comments